Ethical hacking is an authorized attempt to gain unauthorized access to a computer system, application, or data using the strategies and actions of malicious attackers. This practice helps identify security vulnerabilities that can then be resolved before a malicious attacker has the opportunity to exploit them.

What are the key concepts of ethical hacking?
Hacking experts follow four key protocol concepts.
- Stay legal. Obtain proper approval before accessing and performing a security assessment.
- Define the scope. Determine the scope of the assessment so that the ethical hacker’s work remains legal and within the organization’s approved boundaries.
- Disclose the findings. Notify the organization of all vulnerabilities discovered during the assessment, and provide remediation advice for resolving these vulnerabilities.
- Respect data sensitivity. Depending on the data sensitivity, ethical hackers may have to agree to a nondisclosure agreement, in addition to other terms and conditions required by the assessed organization.
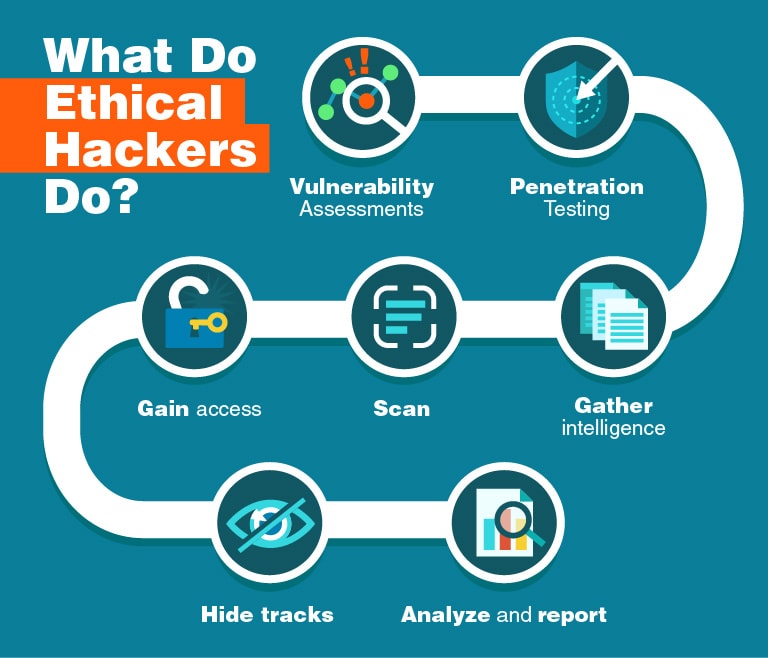
Ethical hackers use their knowledge and skills to secure and improve the technology of organizations. They provide an essential service by looking for vulnerabilities that can lead to a security breach, and they report the identified vulnerabilities to the organization. Additionally, they provide remediation advice. In many cases, ethical hackers also perform a retest to ensure the vulnerabilities are fully resolved.
The goal of malicious hackers is to gain unauthorized access to a resource (the more sensitive the better) for financial gain or personal recognition. Some malicious hackers deface websites or crash back-end servers for fun, reputation damage, or to cause financial loss. The methods used and vulnerabilities found remain unreported. They aren’t concerned with improving the organizations security posture.
What problems does ethical hacking identify?
Ethical hacking aims to mimic an actual attack to look for attack vectors against the target. The initial goal is to perform reconnaissance, gaining as much information as possible. Once an ethical hacker gathers enough information, they use it to look for vulnerabilities. They perform this assessment using a combination of automated and manual testing. Even sophisticated systems can have complex countermeasure technologies that may be vulnerable. In addition to uncovering vulnerabilities, ethical hackers use exploits against the vulnerabilities to prove how a malicious attacker could exploit it.
Some of the most common vulnerabilities discovered by ethical hackers include
- Injection attacks
- Broken authentication and authorization
- Security misconfigurations
- Business logic vulnerabilities
- Use of components with known vulnerabilities
- Sensitive data exposure
- Vulnerability chaining
After the testing period, ethical hackers prepare a detailed report that includes additional details on the discovered vulnerabilities along with steps to patch or mitigate them.
How does SECUNET manage ethical hacking?
Secunet offers managed penetration testing, also known as pen tests, for web applications and services. This security testing technique simulates a real-world attack on a system to identify vulnerabilities and weaknesses in systems and code. Using a blend of manual and tool-based testing, Secunet managed penetration testing services provides a comprehensive assessment of a runtime environment with accurate results and actionable remediation guidance.
By opting for a managed penetration testing service provider, companies get access to security testing experts who can help them understand their security risks, meet compliance requirements, and enable in-house security teams to focus on other objectives.